Explain the differences between desktop and laptop architecture. What features are specific to laptops and laptop displays?
Describe the evolution of laptops into other mobile devices.
Get 15% Discount on your First Order
Explain the differences between desktop and laptop architecture. What features are specific to laptops and laptop displays?
Describe the evolution of laptops into other mobile devices.
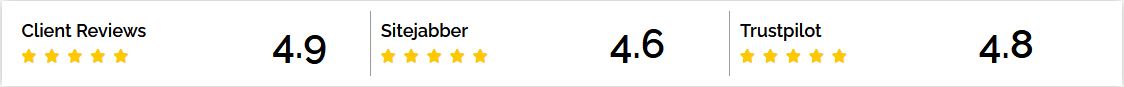
Order a Similar Paper and get 15% Discount on your First Order
Identify at least two ways in which hackers gather information about companies. What can companies do to limit this access, specifically to the ways you have identified? Which type of information can be gathered with enumeration? How and why should companies protect themselves against enumeration attempts?
There is some debate about which is most appropriate. Do an Internet search on opening links in the same browser and then opening links in a new tab and see what you find. Based on what you learned, share in the discussion which side you are on. Should the link
When would you want to create an Azure VM for your company’s network? Tell how you might access the VM if you have one created on your subscription. When you create an Azure VM, is it easy to turn off or remove it from your subscription?
Attached two files , one for the data you will work on in excel file and file discription for the data in PDF As a data scientist please study the data and answer the following questions 1- what is the primerly diagnosis ? 2- What potential risk factors were
Assignment #1 Assignment Submission: Submit your assignment on d2l that has a SINGLE ZIP file that has 1. All Visio Diagrams 2. The PDF document that has all the diagrams and the answers inline below every question including the essay/textual questions. Assignment Deliverables: Provide your answers for the following requirements
FinalProject.pdf Final Project – Credit card numbers and the case of Mobius Duck In this project, you are assisting an investigation. The investigator asked you to help him determine the validity of credit card numbers located in a case of Mobius Duck, case number 20150510-001. Your task is to: –
Project 2: Design the Cloud Deployment Architecture Step 1: Develop User Stories From BallotOnline Employees BallotOnline has decided to move forward with the migration of the email, software development, and backups and archiving workloads to the cloud. You will need to have a good understanding of what users really need
Your job is to: 1) implement the one algorithm in these files that is not already implemented (merge sort), 2) Tell me in a comment in your code three things: what the runtime of this algorithm is whether it is “destructive” whether it is “in-place” 3) submit timing data
attached file Discussion 1: desirable properties of a generative model Comment on what makes a generative model a good model: 1. How is discriminative modeling different from generative modeling? 2. How is generative modeling different from statistical modeling? Assignment 1: multilayer perceptron for images – Deadline 05/12/2024 See the code that
This is a challenging assignment, but I am hoping you will have FUN with it! You must find a news or journal article that is evidence that the problem or issue you wish to study is something current and of concern. Please download and use this template. (Save it per the video “How
In this discussion, you are going to research Vigenere Cipher. Use the Vigenere Table to encrypt the message using the key ORANGE: Hard work always pays. Now use the same key, to decrypt this message: Oktnio ok dncr Instructions: 1. Ignore all cases and punctuations 2. Do not encrypt or decrypt
Prepare the peer’s presentation topic by finding and reviewing the Internet resources and documents about the topic that you are assigned to review. Prepare for your feedback and questions that you will raise throughout the presentation. provide feedback to your peer. Ask your questions, critique the presentation, and make
file attached. 1 Week 1 – Discussion: AI in Business Consider what you have read so far in the learning materials for Week 1, and write a one-page summary about it. Focus on the use of Artificial Intelligence in Business. The summary must present your understanding in your own words
The Enterprise Architecture Repository is an online, web-based platform designed to store and organize Enterprise Architecture artifacts produced by EA software tools. You work as a developer for CMS and want to protect the security of the organization. You have developed a level of trust with the development team,
Instructions: Q1. Design a program that asks the user to enter a series of 20 numbers. The program should store the numbers in a list then display the following data: The lowest number in the list The highest number in the list The total of the numbers in the list The
IT543-4: Design an implementation of cryptographic methods for an organization. Assignment Instructions: Perform the lab described in the zip folder Wireshark — Capturing SSL Packets. Follow the directions, perform the indicated instructions, and provide the requested information. Take screenshots of each step to show that you are working through the steps.
Discussion The unit readings outline several challenges of implementing and upgrading enterprise information systems. Employees were cited as one of the pain points. Why do you think this is? As an MIS leader responsible for implementing or upgrading an enterprise information system, select two or three strategies you would use
You must find a news or journal article that is evidence that the problem or issue you wish to study is something current and of concern. Please download and use this template. (Save it per the video “How to Save and Submit Assignments, in two formats. Submit the file
Our support team is here 24/7 via live chat, phone and on-line support ticketing system.

©2023 All Rights Reserved. SpeedyEssayelp.com